Security Risk Models for Cyber Insurance: A Comprehensive Guide

Cyber insurance has become increasingly important as businesses face growing threats from cyberattacks. A key component of cyber insurance is the security risk model, which helps insurers assess the risk of a business being targeted by a cyberattack and determine the appropriate premium.
There are a number of different security risk models used by insurers, each with its own strengths and weaknesses. This article will discuss the different types of security risk models and how they are used in cyber insurance.
There are two main types of security risk models: quantitative and qualitative.
4.4 out of 5
| Language | : | English |
| File size | : | 4502 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 273 pages |
- Quantitative models use mathematical formulas to calculate the risk of a cyberattack. These models typically consider factors such as the business's industry, size, and security controls.
- Qualitative models use expert judgment to assess the risk of a cyberattack. These models typically consider factors such as the business's security culture, employee training, and incident response plans.
Both quantitative and qualitative models can be used to assess the risk of a cyberattack. However, quantitative models are generally more objective and can be used to compare the risk of different businesses. Qualitative models are more subjective and can be more difficult to compare.
Security risk models are used by insurers to assess the risk of a business being targeted by a cyberattack. This information is used to determine the appropriate premium for the business's cyber insurance policy.
The premium for a cyber insurance policy is based on a number of factors, including the business's:
- Industry
- Size
- Security controls
- Claims history
- Credit rating
The security risk model is used to assess the business's risk of a cyberattack. This information is then used to determine the appropriate premium for the business's cyber insurance policy.
There are a number of benefits to using security risk models in cyber insurance. These benefits include:
- Improved risk assessment: Security risk models help insurers to assess the risk of a cyberattack more accurately. This information can be used to make better decisions about pricing and coverage.
- Reduced premiums: Businesses that have a strong security risk model can often qualify for lower premiums on their cyber insurance policies.
- Improved security posture: Security risk models can help businesses to identify and address their security weaknesses. This can help to improve their overall security posture and reduce the risk of a cyberattack.
There are also some challenges to using security risk models in cyber insurance. These challenges include:
- Data availability: Security risk models require a lot of data to be effective. This data can be difficult to collect and may not be available for all businesses.
- Model complexity: Security risk models can be complex and difficult to understand. This can make it difficult for businesses to use the models to make informed decisions about their cyber insurance coverage.
- Model accuracy: Security risk models are not always accurate. This can lead to businesses being overcharged for their cyber insurance premiums or being denied coverage altogether.
Security risk models are a valuable tool for insurers and businesses that are looking to purchase cyber insurance. These models can help to improve risk assessment, reduce premiums, and improve security posture. However, there are also some challenges to using security risk models. Businesses should be aware of these challenges before using a security risk model to make decisions about their cyber insurance coverage.
4.4 out of 5
| Language | : | English |
| File size | : | 4502 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 273 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Glossary
Glossary Bibliography
Bibliography Scroll
Scroll Classics
Classics Biography
Biography Autobiography
Autobiography Reference
Reference Encyclopedia
Encyclopedia Character
Character Resolution
Resolution Librarian
Librarian Catalog
Catalog Card Catalog
Card Catalog Borrowing
Borrowing Stacks
Stacks Reserve
Reserve Reading Room
Reading Room Rare Books
Rare Books Special Collections
Special Collections Interlibrary
Interlibrary Thesis
Thesis Dissertation
Dissertation Awards
Awards Reading List
Reading List Book Club
Book Club Theory
Theory Jan Camp
Jan Camp Sergio J Lievano
Sergio J Lievano Phyllis T Smith
Phyllis T Smith Christopher G Nuttall
Christopher G Nuttall Carol Montparker
Carol Montparker Clyde Wilcox
Clyde Wilcox Chaplain Stephen Dicks
Chaplain Stephen Dicks Helena Silverstein
Helena Silverstein Rob Mundle
Rob Mundle John Howard Yoder
John Howard Yoder Mark J Smith
Mark J Smith Ledecky Fun Press
Ledecky Fun Press Michael Garlock
Michael Garlock Guns N Roses
Guns N Roses Yoshiki Nakamura
Yoshiki Nakamura Chris Welch
Chris Welch Susan Huxley
Susan Huxley Ezra Levant
Ezra Levant Andrew Kolasinski
Andrew Kolasinski Elliott Lewis
Elliott Lewis
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Gene PowellSal Gabrini: The Burning Love That Fueled His Culinary Empire | Sal Gabrini's...
Gene PowellSal Gabrini: The Burning Love That Fueled His Culinary Empire | Sal Gabrini's... Miguel NelsonFollow ·16k
Miguel NelsonFollow ·16k Jermaine PowellFollow ·16.5k
Jermaine PowellFollow ·16.5k Gavin MitchellFollow ·2.8k
Gavin MitchellFollow ·2.8k Ian PowellFollow ·11.8k
Ian PowellFollow ·11.8k Lawrence BellFollow ·2.4k
Lawrence BellFollow ·2.4k Jonathan FranzenFollow ·12.7k
Jonathan FranzenFollow ·12.7k Ray BlairFollow ·3.2k
Ray BlairFollow ·3.2k Asher BellFollow ·16.8k
Asher BellFollow ·16.8k
 Carson Blair
Carson BlairMy Second Chapter: The Inspiring Story of Matthew Ward
In the tapestry of life, where threads...
 Graham Blair
Graham BlairFull Voice Workbook Level Two: A Comprehensive Guide to...
The Full Voice Workbook Level Two is a...
 Darren Blair
Darren BlairEmbark on an Unforgettable Adventure: Exploring the...
Prepare yourself for an extraordinary...
 Isaiah Powell
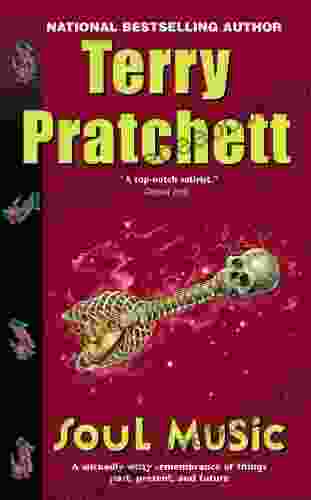
Isaiah PowellSoul Music: A Literary Odyssey Through Discworld
In the realm of fantasy...
4.4 out of 5
| Language | : | English |
| File size | : | 4502 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 273 pages |